Face masks are now front line in the fight against a global pandemic that has disrupted nearly all human life. Meanwhile contact-less solutions have become a best practice for avoiding disease transmission at retail point-of-sale, medical patient check-in, banking access, food distribution, and other essential activities. All three mainstream biometric modalities (face, fingerprint, and iris), which often empower these activities, experience unique challenges in the context of a pandemic:
- Fingerprint technology is potentially a disease transmission vector unless it is contactless, in which case there are challenging hardware requirements.
- Iris recognition is not impacted by masks, but it cannot work with visible light cameras and instead requires near-infrared sensors that can be difficult to acquire at scale and are often not interoperable.
- Face recognition, while surprisingly good in the presence of partial facial occlusions, exhibits a loss in accuracy and reliability for individuals wearing medical medical masks.
A brief history of periocular recognition
Periocular recognition is one solution that can deliver better accuracy, ease-of-use, and safety, while not suffering from the same drawbacks of onerous sensor requirements, usability or occlusions of other modalities.
The first periocular recognition algorithm was introduced by Unsang Park, Arun Ross, and Anil Jain in 2009 [1] [2] in order to augment the capabilities and challenges of iris recognition algorithms. At the time of their seminal work, iris recognition was in the midst of meteoric growth due to its accuracy and speed. Challenges in sensor interoperability and user-experience eventually slowed the adoption of iris recognition, though iris recognition is still a powerful and widely deployed biometric modality. It can also easily be paired with face recognition for robust multi-modal identification.
Perhaps it was the slowing of iris recognition (and the growth of face recognition) that stinted the adoption of periocular recognition, but, regardless of why it never gained mainstream adoption, the fact is that today there is only one other commercial offering for periocular recognition.
Next generation periocular recognition
Today, with the release of the ROC Periocular algorithms, accurate identification can be achieved using solely the eye and eyebrow regions of the face. This is made possible through the same breakthroughs in deep convolutional neural networks and best-in-class software packaging that enable Rank One to deliver both high accuracy and hardware efficiency in the ROC SDK’s face recognition algorithms.
The first step of the ROC Periocular algorithm is to detect a person based on their eyes and eyebrows. The following images demonstrate the output of the ROC Periocular detection algorithm on masked faces:
In the above examples, the periocular detector is able to rapidly detect a person, despite them wearing a mask. This successful person detection is one of the most profound ways that periocular recognition can outperform conventional face recognition in the presence of masked faces. That is, one of the biggest challenges presented by masks is that the initial face detection algorithms will have a higher incidence of failure. Known as failure-to-detect, or failure-to-enroll, if a biometric template cannot be created due to a failed detection, no identification can take place.
Once the periocular region of the face has been detected, it can then be processed to locate and represent the salient morphological features into a feature vector template. This representation process involves tens of millions of mathematical computations. And, similar to face recognition algorithms, the time required to perform this step can vary quite significantly based on a vendor’s ability to engineer efficient software. In the case of the ROC Periocular algorithm, this representation process is faster than the standard ROC FR algorithm, itself renowned for its industry-leading efficiency.
The template produced by the ROC Periocular algorithm can be used in the same manner as a ROC FR template, which includes the common tasks of 1:1 identity verification or 1:N identification.
The ROC Periocular algorithm has been benchmarked for accuracy and efficiency against ROC SDK v1.20:
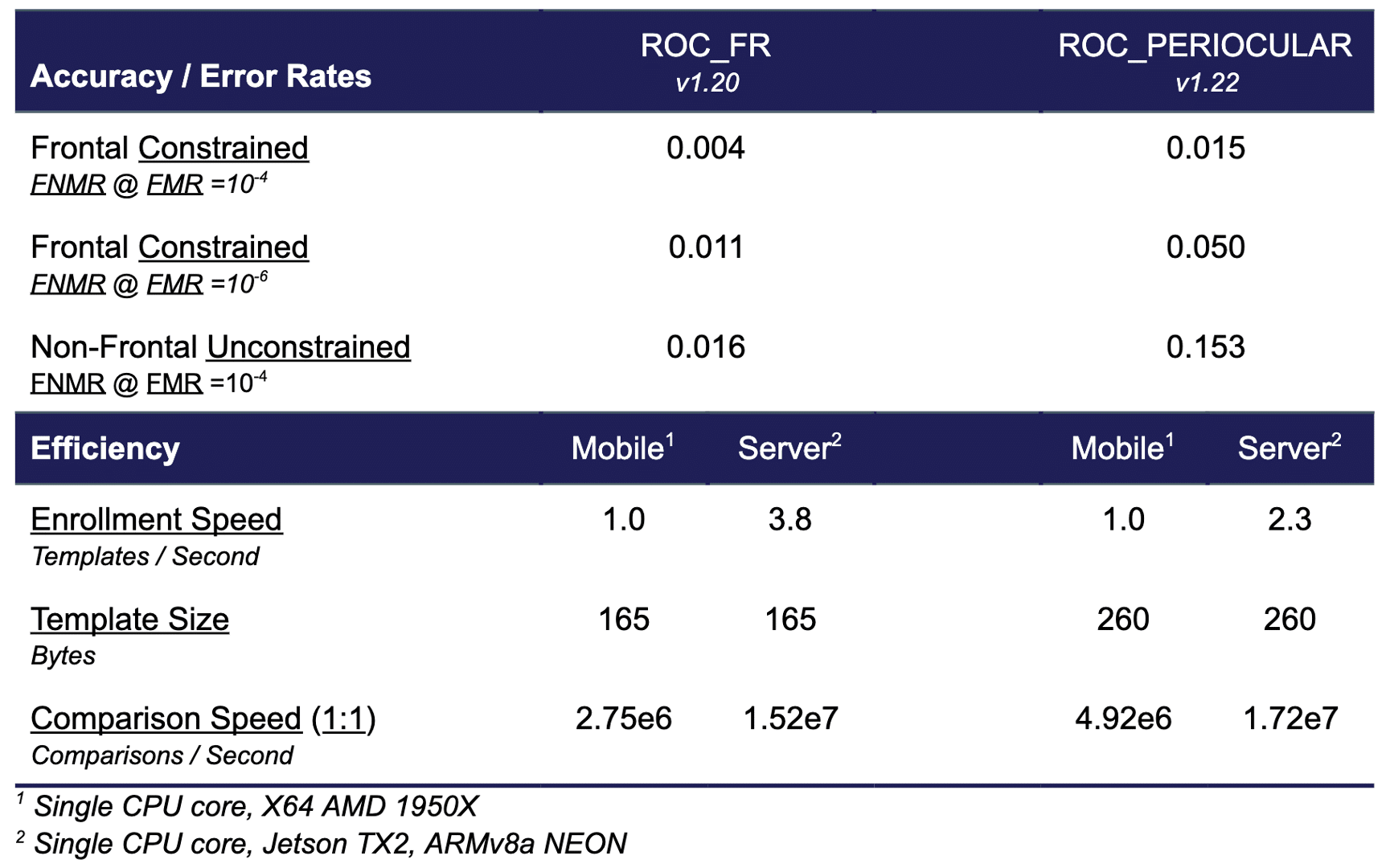
It is worth noting the following:
- The “non-frontal unconstrained” dataset includes sunglasses in 7% of the images. As periocular recognition cannot reliably be used to recognize persons with sunglasses, the error rate for the periocular algorithm on this dataset is 7% greater than it would be if no sunglasses were present (but other unconstrained challenges remained).
- The enrollment speed of the periocular algorithm, while still faster than most NIST FRVT face recognition algorithms, does not currently possess Rank One’s hallmark efficiency. This is due to the urgency of releasing this algorithm in an accelerated manner due to the crisis presented by COVID-19.
- The accuracy of the periocular is roughly the same as the ROC face recognition algorithms were in early 2018. Which means this periocular algorithm would have outperformed a large number of NIST FRVT face recognition algorithms two years ago. Further, as many critical systems are running outdated face recognition algorithms due to a lack of evergreen licensing, the ROC Periocular algorithm is likely more accurate than certain face recognition systems powering national security and critical infrastructure applications.
API and Licensing
The API of the ROC Periocular algorithm is nearly identical to the ROC FR algorithm. Similar to how users can switch between the ROC FR and ROC FR Fast algorithms, the ROC Periocular algorithm can be used by simply changing an input flag into the ROC Represent template generation function. For current Rank One partners this means the periocular algorithm can be integrated by changing as little as one line of code. For future Rank One partners, note that the Rank One API is industry renowned for its simplicity and thoughtful design.
Additional API features will be provided to enable the ROC Periocular algorithm to easily be combined with the ROC FR algorithm. Thus, an integrator can use ready-made API functions to configure their system to attempt to leverage the full face biometric, and instead switch to the periocular biometric if a mask is present.
In terms of licensing, the ROC Periocular algorithm is made available as part of the standard features available in a ROC SDK license. Thus, any current license under active maintenance, or any new license purchase, will come equipped with the ROC Periocular algorithm.
Periocular or Face Recognition?
Whether or not use periocular recognition or face recognition is dependent on the specific application, use-case, and/or environmental factors encountered by a given system. For example, if it is known that all persons interacting with a system will be wearing a mask, then it makes sense to use the periocular algorithm.
And, while face recognition does still work in the presence of a mask, it is important to realize that in the presence of masks, in the best case, a face recognition algorithm would generalize into a periocular recognition algorithm, as that is the only information available. However, in the worst case, face detection will fail, same-person comparisons will have lower similarity scores, or different-person comparisons will have higher similarity scores.
By providing its user community with access to both face and periocular recognition algorithms, and further providing API features to enable these two modalities to be easily used in tandem, contactless identification systems can be designed that cover the breadth of environmental factors present in the midst of the global pandemic.
Please contact our team to begin an evaluation of the ROC Periocular algorithm.
[1] U. Park, A. Ross, and A. K. Jain, “Periocular Biometrics in the Visible Spectrum: A Feasibility Study”, 3rd Intl Conf. on Biometrics: Theory, Applications and Systems, Washington DC, September 2009.
http://biometrics.cse.msu.edu/Publications/Face/ParkRossJain_Periocular_BTAS09.pdf
[2] U. Park, R. Jillela, A. Ross and A. K. Jain, “Periocular Biometrics in the Visible Spectrum”, IEEE Transactions on Information Forensics and Security, Vol. 6, No. 1, pp. 96-106, March 2011.
http://biometrics.cse.msu.edu/Publications/GeneralBiometrics/ParkJillelaRossJain_PeriocularBiometrics_VisibleSpectrum_TIFS10.pdf